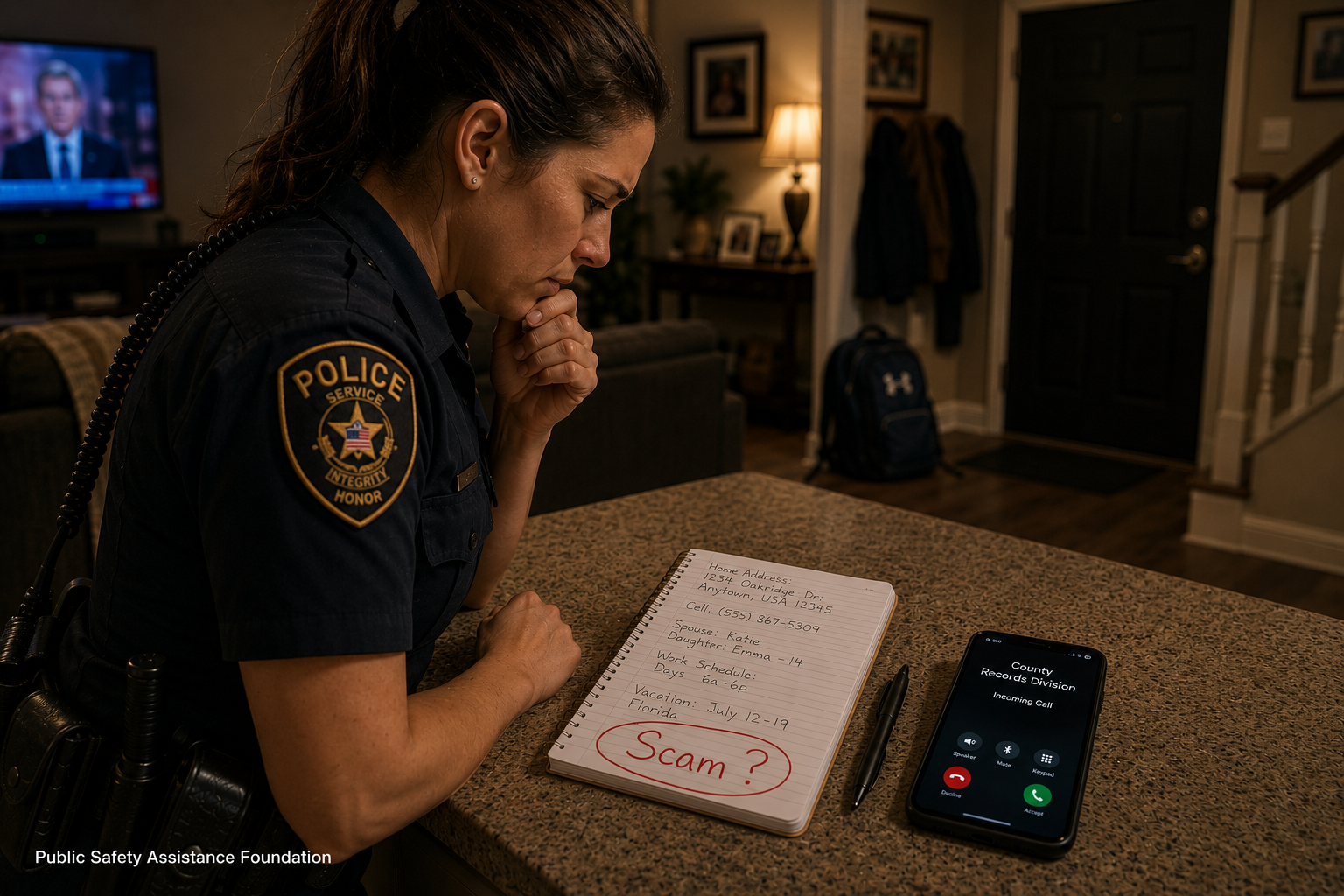
⚠️ The Danger of Believable Scams
There was a time when scams were easy to spot. Misspelled emails. Poor grammar. Obvious fake websites. Strange overseas phone
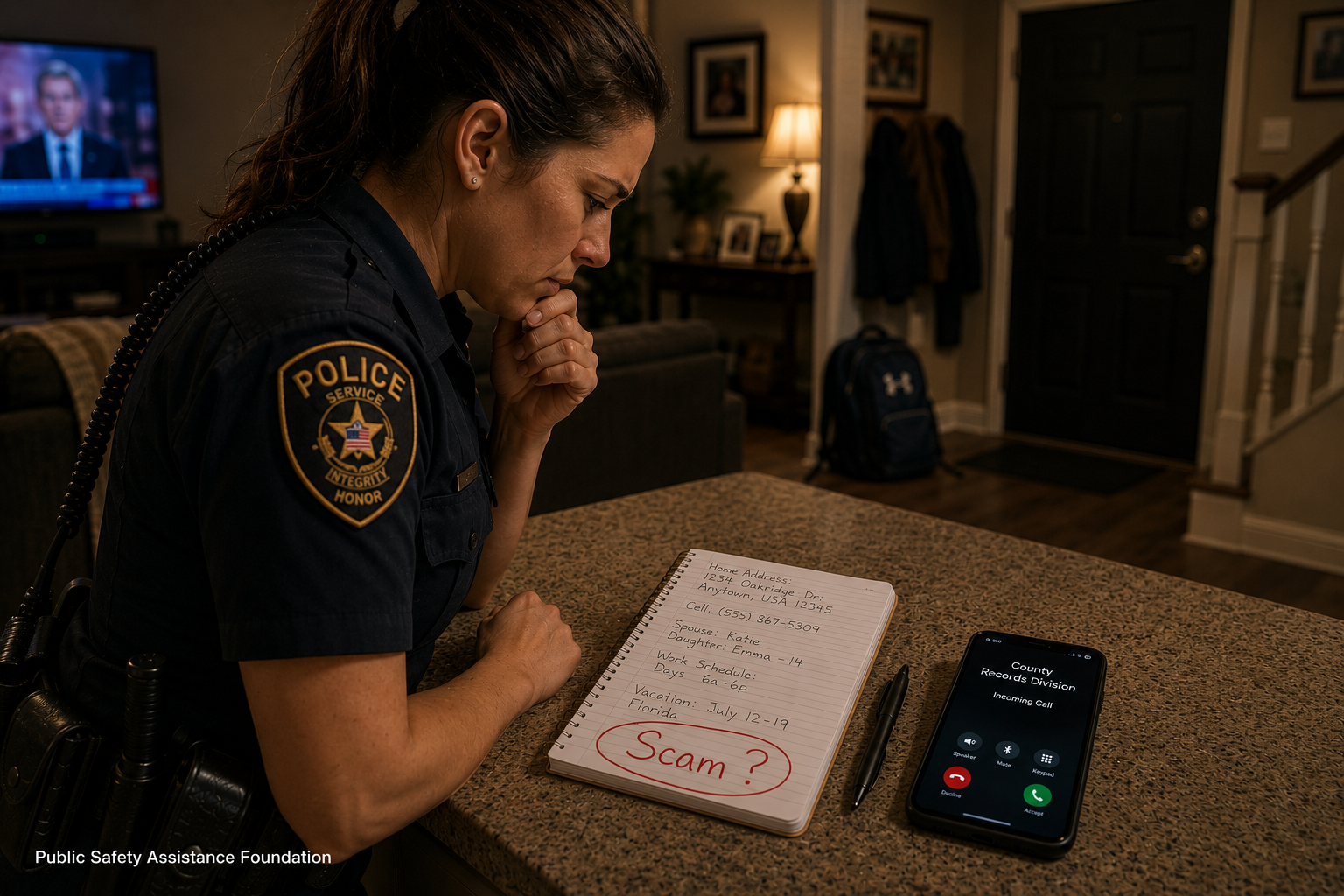
There was a time when scams were easy to spot. Misspelled emails. Poor grammar. Obvious fake websites. Strange overseas phone

For decades, conversations about supporting law enforcement officers focused primarily on what happened in the field. Discussions centered around staffing

Across the country, law enforcement officers are increasingly encountering individuals recording public interactions for social media, livestreams, and so-called “First

Every May, communities across the country pause to recognize National Police Week and Peace Officers Memorial Day, observed annually on
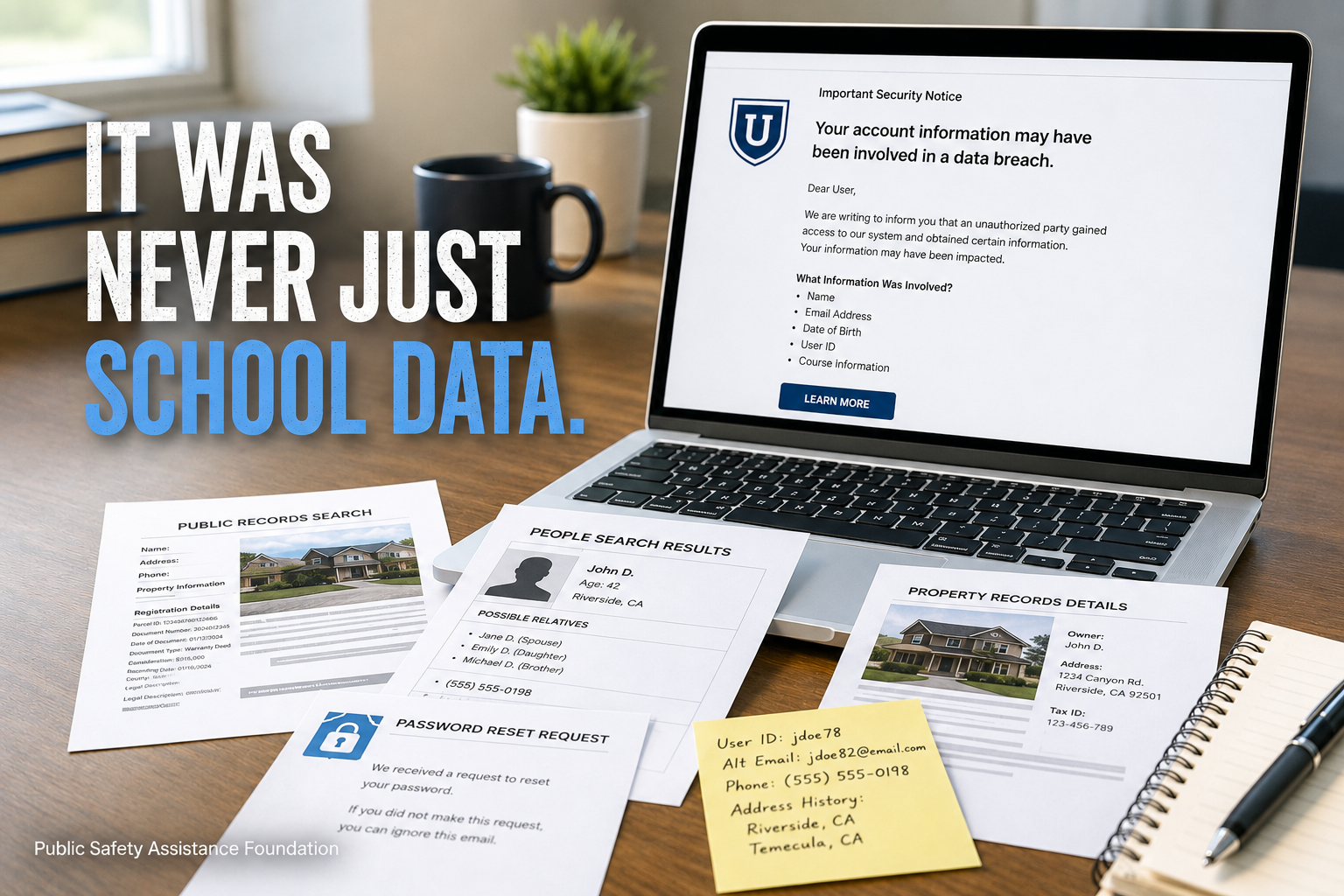
Students across the country logged into their school accounts expecting to prepare for finals. Instead, many were met with something

When people think about online privacy protection for law enforcement officers and public officials, the conversation usually starts with threats.

The most experienced law enforcement officers know something that often goes unnoticed outside the profession. Good preparation rarely looks dramatic.

Families headed to the zoo expecting a normal afternoon. Children were excited. Staff members were guiding guests through exhibits. Security

It doesn’t take long. In fact, it happens faster than most people realize. The moment someone types your name into